Status: Alert not Alarmed
Australia and New Zealand had a relatively quite fortnight on the cyber threat landscape, in terms of what we have visibility into using open sources.
The most notable event was the multiple fake breach and leak claims made against Australian State and Federal governments by Indonesian hacktivists. These claimed attacks can cause fear and uncertainty if projected widely by the threat actors and can result in internal responses by organizations that can impact resources, so challenging them publicly can quickly diminish that influence.
Hacktivist Activity - 12 Victims
11 February - Australia
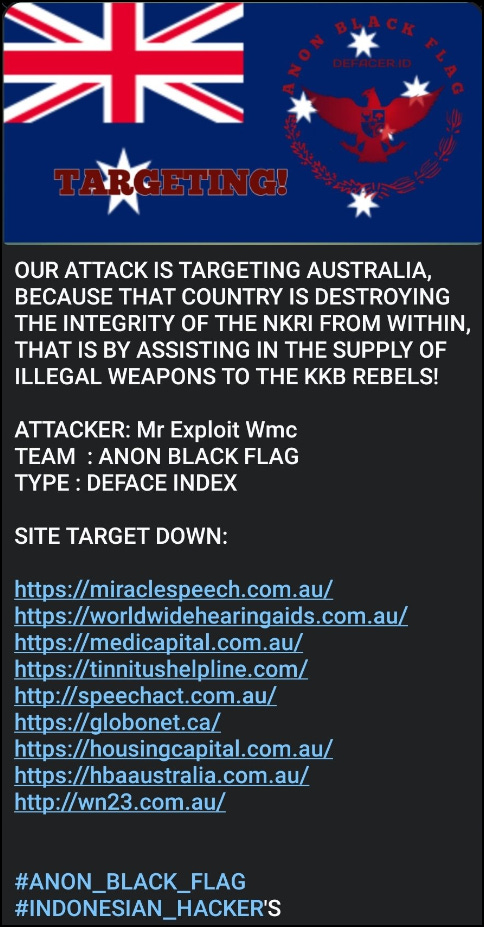
Anon Black Flag Indonesia conducted DDoS attacks on multiple Australian websites - motivated by the fake theory that the Australian government is funding rebels in West Papua.
13 February - Australia
Toxcar Cyber Team from Indonesia claimed to breach and leak documents from the South Australian government. These turned out to be publicly accessible via a Google search. This is becoming standard practice for the group.
13 February - Australia
Toxcar Cyber Team from Indonesia claimed another breach and leak, this time of the Australian government. This is the second time the group has claimed to have hacked the Australian Parliament website. The reality is that they are screenshotting the publicly accessible information from the site.
13 February - Australia
Padang System Error conducted DDoS attacks on a range of Australian small/medium business websites.
13 February - Australia
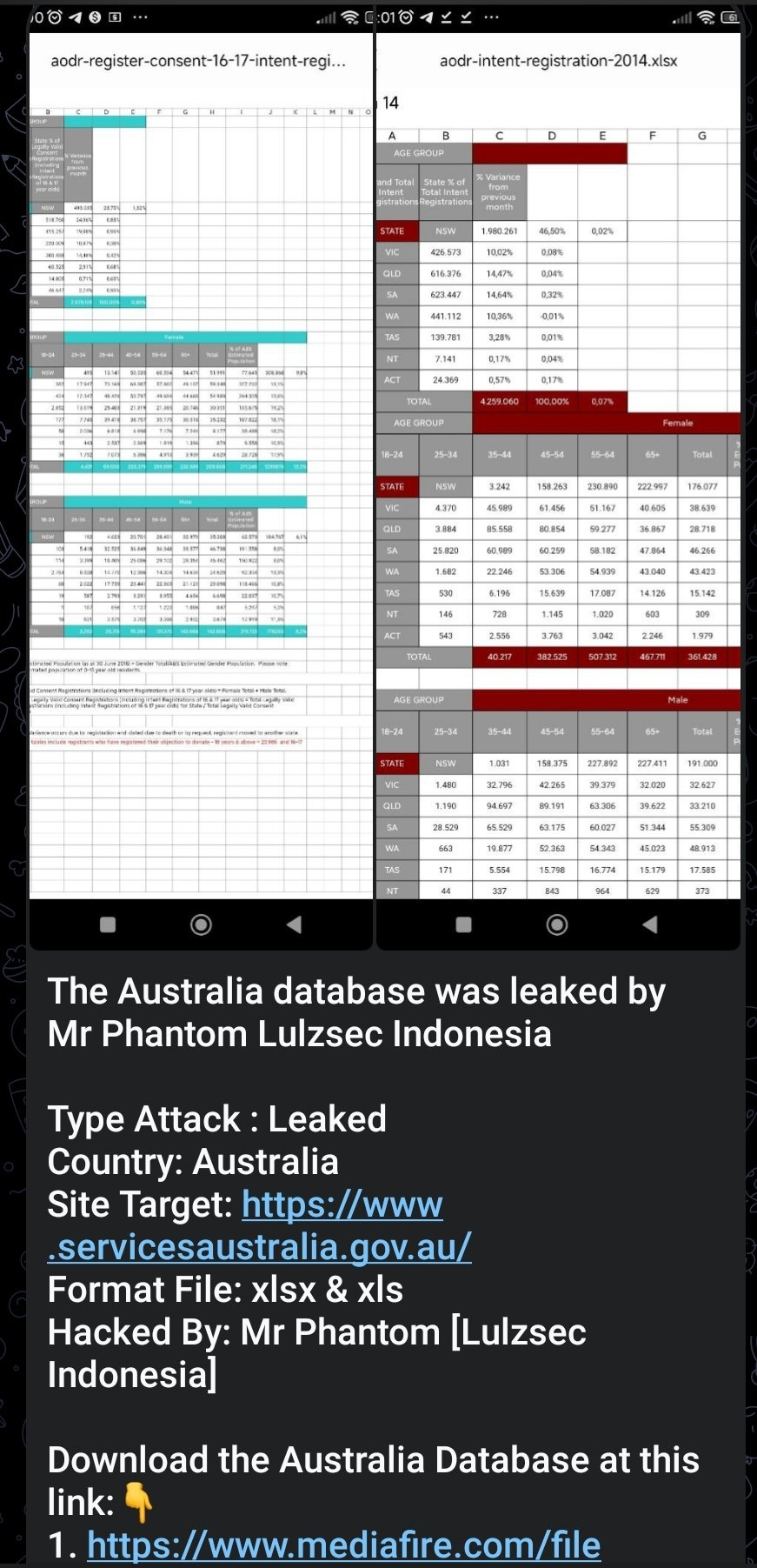
Lulzsec Indonesia conducted a fake data breach of Australian Government data. This is a great example of when a hacktivist group conducts a fake breach and leak attack to push an infoops narrative and also, why we need to push back with timely and contemporary Situational Awareness.
Image 1 above , is the claim of the breach by Lulzsec Indonesia - both images are excel files that clearly show the name of the document. A brief Google search shows that both these documents are publicly accessible.
I have also reviewed the files they claim to have, and these are just the same open source spreadsheets. While the capability does not appear to backup the claimed breach - the intent remains extremely high and these claims can have knock-on impacts such a reputational and trust impacts on the organization. It is very unlikely that Lulzsec Indonesia has had any impact on the Australian Government.
Ransomware - 2 Victims
6 February - New Zealand
8Base ransomware gang posted YRW Limited - Chartered Accountants to their leak site.
12 February - Australia
Medusa ransomware posted Kadac Australia to their leak site.
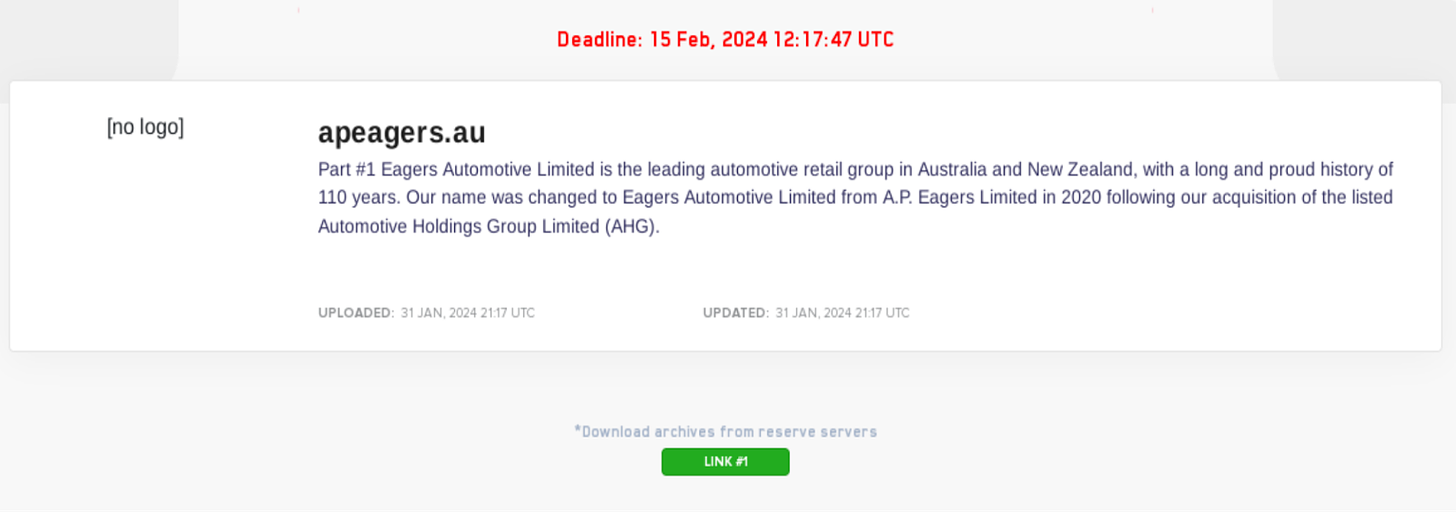
Update on Eagers Automotive - Australia
After being posted to the LockBit leak site on 30 December 2023, the data of Eagers Automotive Limited has now been released after the 15 February 2024 deadline lapsed. The leak appears to include audit, payroll, finance and insurance, and other information, possibly from as early as 2021. Now that it is publicly accessible, the potential sensitivity of the data raises concerns that this breach may have knock-on effects for customers, as well as individual car dealerships.
Eagers Automotive has since released a market announcement/update to the ASX, stating that the company has “become aware” of the leaked data on the LockBit leak site and that it is now “investigating this claim as part of its ongoing response, which is expected to take some time to complete.” Eagers Automotive has also reiterated their message from their January update that the cyber incident is not expected to be material for the 2024 Financial Year.” To date, no information relating to the initial access vector has been released by the company or any media outfits.
Eagers Automotive is one of the largest operators of car dealerships in Australia and New Zealand, and employs 8,500 people. In the first half of 2023, it reported revenues of AU$4.82 billion. The cyber attack
Underground posts/mentions of Note
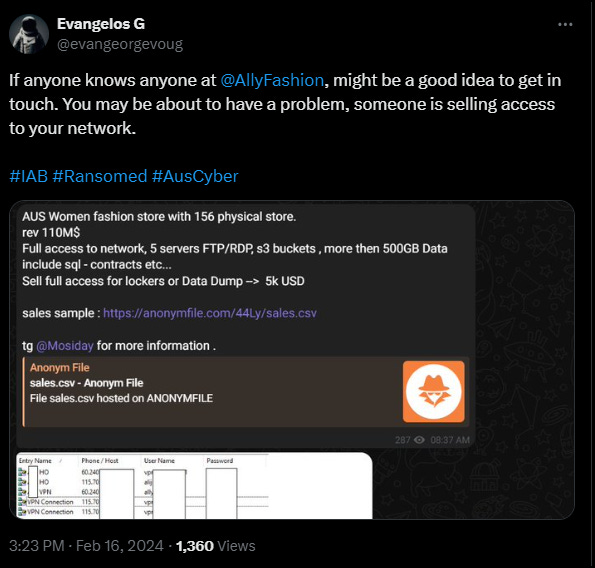
Australian security researcher, https://twitter.com/evangeorgevoug reported that it was likely that Ally Fashion was the victim that had network access available for sale by an IAB.
For regular updates on the Australian and New Zealand cyber threat landscape follow: