As promised in the last edition we are now back to a regular two weekly cadence for this series.
If you read anything below that you would like to know more about, please reach out and we will either get you the answers or someone who can provide them. The whole aim of this newsletter is to capture what the cyber threat landscape looks like for Australia - we share a mix of publicly presented information and some insights from underground forums.
Israel-Hamas War implications for Australia
TLDR
It is unlikely that Australia will see any impacts in cyberspace as a result of increased middle-eastern tensions in the short to medium term. It is unlikely that Australia will experience any cyber related activity in the next month as a result of the ongoing Israel situation.
Observing hacktivist operations in the context of Russia’s invasion of Ukraine, it has become apparent that these groups are highly reactive to media reporting concerning Western-aligned responses to conflict. For example, the pro-Russian group NoName057(16) has targeted Australian entities with DDoS attacks twice in 6 months, with both attacks claimed by the group to have been in response to the Australian Government announcing further military aid to Ukraine. Similarly, hacktivist groups on both sides of the Israel-Hamas conflict will be watching the official statements from Australia and other Western-aligned countries closely. These groups will likely also be highly reactive to any public statements from Australian companies, or if they were seen to be providing any level of support to either side during the conflict. To date, Australia’s diplomats and foreign ministry have offered limited responses to the conflict, though this may change in the coming days and weeks.
Ransomware
Notably quite on the ransomware front for Australian organizations being posted as victims to leak sites with just one organization.
This does not indicate a change in opportunistic targeting from extortion groups, it is simply just a two-week period when only one organization was posted.
6 October
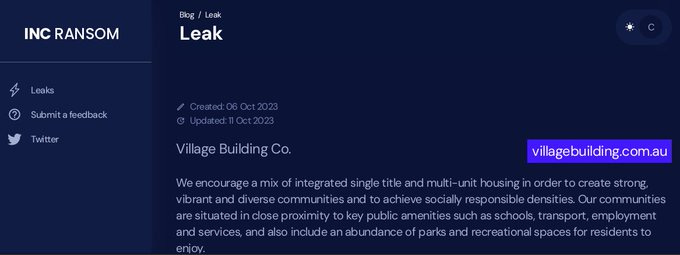
INC Ransom posted Village Building Co. To their leak site
Underground posts/mentions of note
7 October
A user on Breachforums posted an Australian skip bin company database and network access for 8 forum credits.
10 October
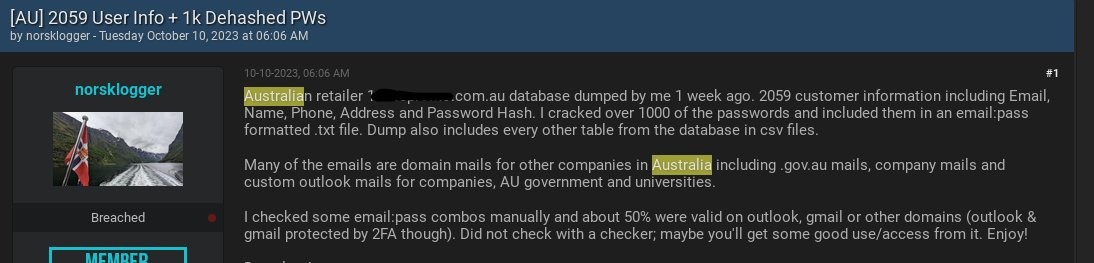
A user on Breachforums claims to have dumped a database from a custom merchandise company in Australia. They claim the exposed email addresses include .gov.au accounts (We have not reviewed the data)
13 October
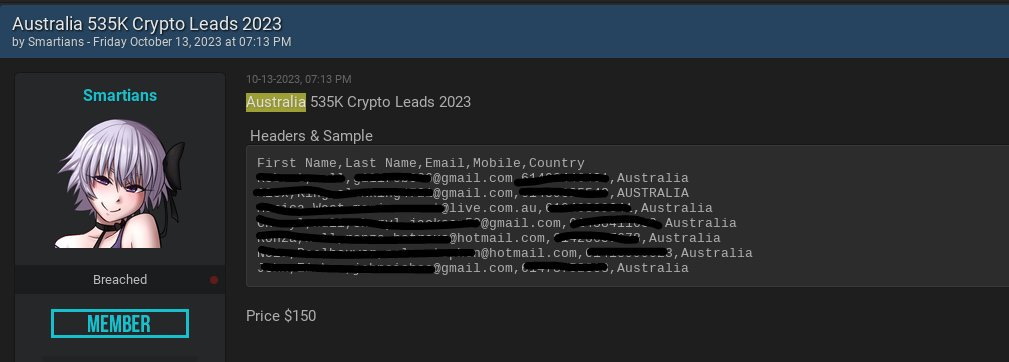
A user on Breachforums is claiming to have over 535,000 Australia crypto leads for sale. These datasets can often be a series of previously exposed credentials put together in an attempt to get quick forum credits or financial payments.
13 October
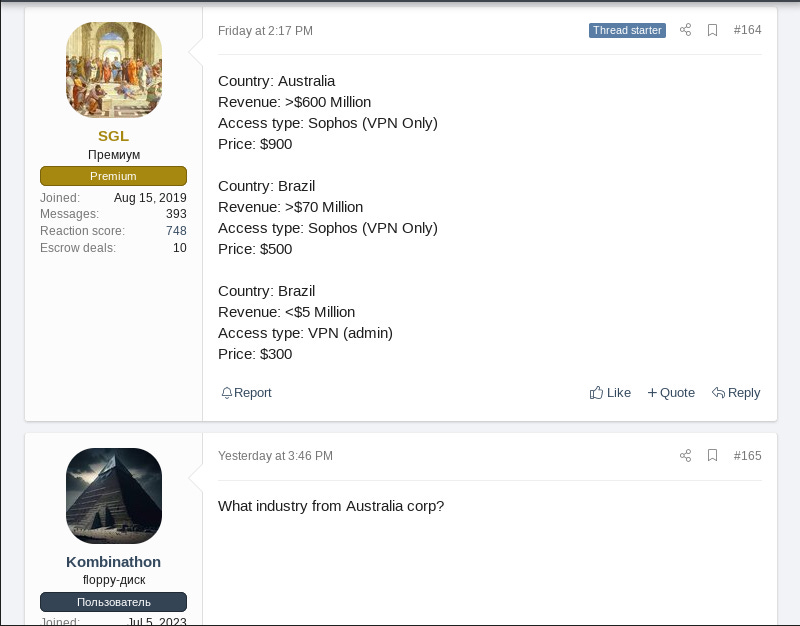
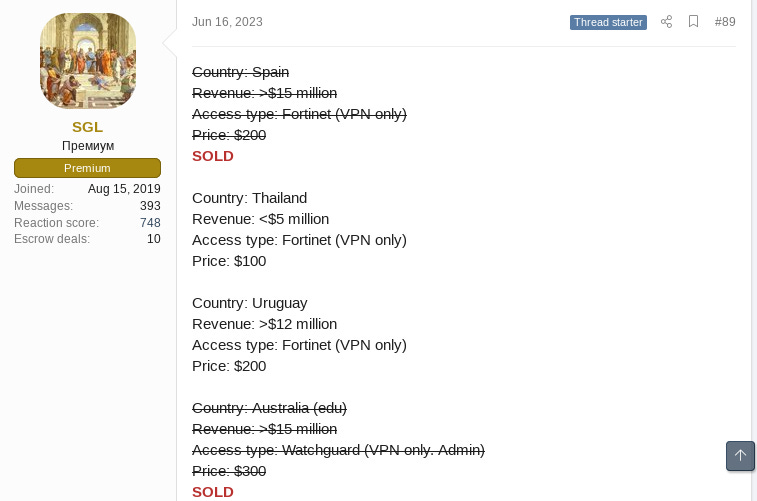
SGL, a member of the Russian-speaking forum XSS, advertised network access to an Australian organization with an annual revenue of over $600 million.
Access to the unknown company’s Sophos Connect SSL VPN is being offered for $900.
SGL is an initial access broker with a strong reputation on XSS, having made 10 deals through the forum’s escrow service and attracting a number of upvotes and positive feedback from other members.
Among SGL’s successful sales is VPN access to two Australian companies: an education entity with over $15 million in revenue in June 2023 and an unknown smaller company with less than $5 million revenue in July 2023.
There is no evidence that SGL has sold network access to any known ransomware affiliates, but an access broker that operates on a high tempo will always be valuable to a financially-motivated group.
It is possible that SGL makes use of compromised corporate credentials for initial access to VPN authentication domains, performing basic reconnaissance once in a network to determine the network owner, and selling access on if it is able to be monetized.
If you have any additional insights or questions please reach out to: