Status: Alert not Alarmed
The past two weeks in the Australian cyber threat landscape have been dominated by hacktivist activity. It was always possible that Australia would see some activity as a result of support for Israel and our alliance structure. It was not clear if Australia had a ‘real chance’ of seeing hacktivist activity, but the speed of spread from anti-Israel hacktivist groups to target countries outside of Israel was rapid and shows that no one example of hacktivist activity is the same as another. We continue to track and monitor these activities and provide continual updates on X(Twitter).
Hacktivist Activity
20 October
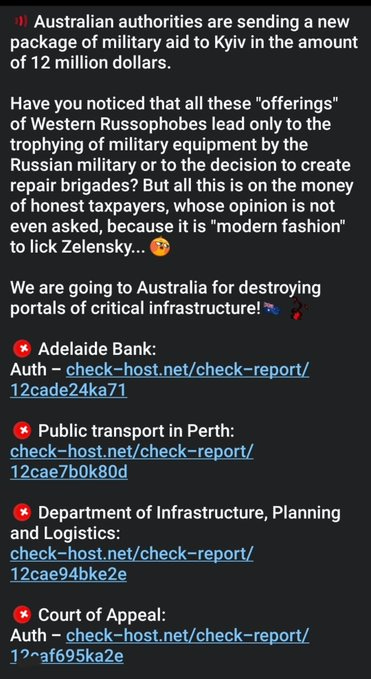
We wrote a full report about the declared global campaign by IRoX Team, who was declaring a sustained 10 day campaign against various countries, including Australia. This was the first threat made against Australia.
The group has not yet claimed any attacks against Australia.
22 October
Infinite.ID conducted the first claimed attack against Australia by anti-Israel hacktivists since 7 October. The attack was a fake breach and leak attack, these are popular with hacktivist groups. This one was likely to be old stolen data possibly taken from an underground forum for free. The ‘evidence’ was a video of the data.
23 October
Team_Insane_Pakistan targeted Optus Stadium in Perth with a DDoS attack. They claim it was ‘for fun’ however, the group is very vocal about their support of Pakistan cricket and Australia had beaten them recently in the ODI World Cup.
24 October
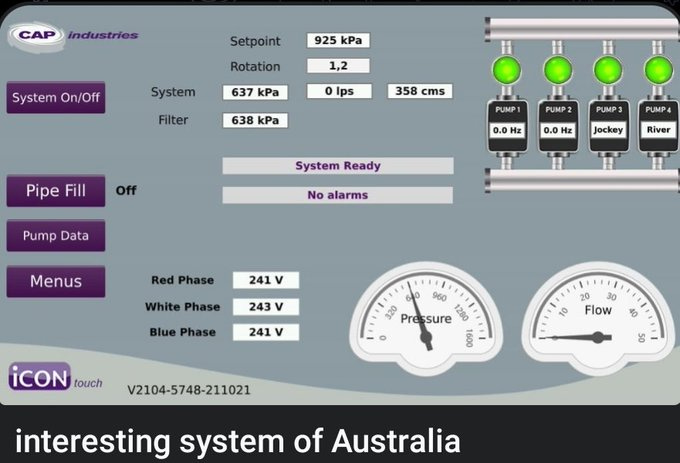
Ghost Clan Malaysia shared a screenshot of a control system they claimed was from Australia - no further information.
25 October
TengkorakCyberCrew defaced an Australian building company.
25 October
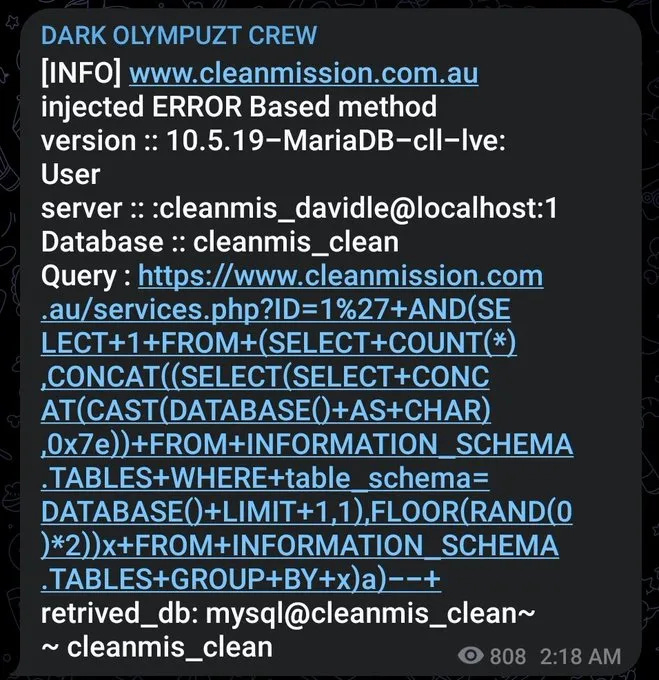
Dark Olympuzt Crew claimed to dump the database of clean mission Australia.
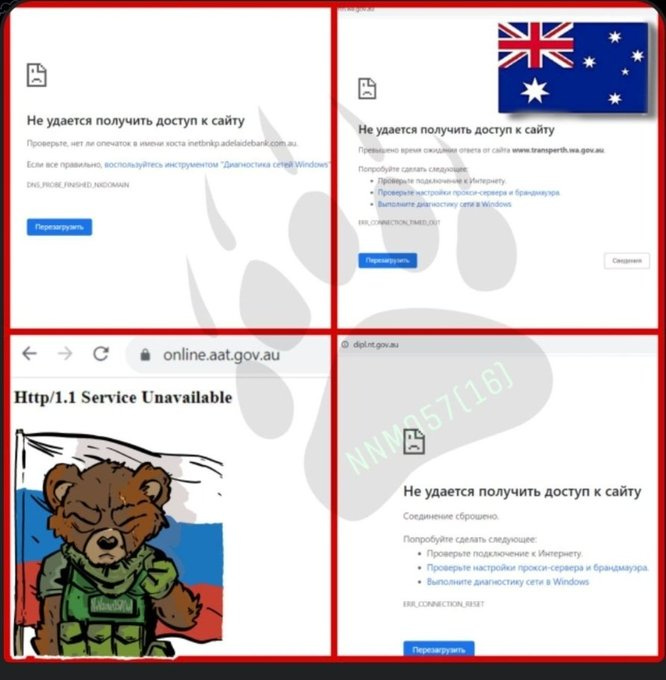
26 October - Pro-Russian hacktivist attacks
Noname057(16) - the most active pro-Russian hacktivist group targeted several Australian critical infrastructure and government websites with DDoS attacks as a result of continued Australian support for Ukraine. The attacks were a one-off and not a sustained campaign.
26 October
AnonGhost Indonesian made a threat against Australian government infrastructure, currently the group has not claimed any attacks.
26 October
IRoX Team declared they were starting their attacks on Australia, but at time of writing they have no provided any evidence to their telegram group (while it is mostly the policy of these groups to share attacks, just because we don’t see evidence does not mean they aren’t active)
26 October
Ganosecteam claimed to deface 6 Australian websites - which turned out to be two. As with most deface attacks they were against websites of small and medium businesses.
27 October
Hacktivist Aceh claimed to be conducting a new wave of attacks on countries including Australia - they stated they would not be sharing the results on their telegram. This is unusual behavior, as a main goal of hacktivism is to share and advertise attacks to try and evoke societal chaos.
29 October
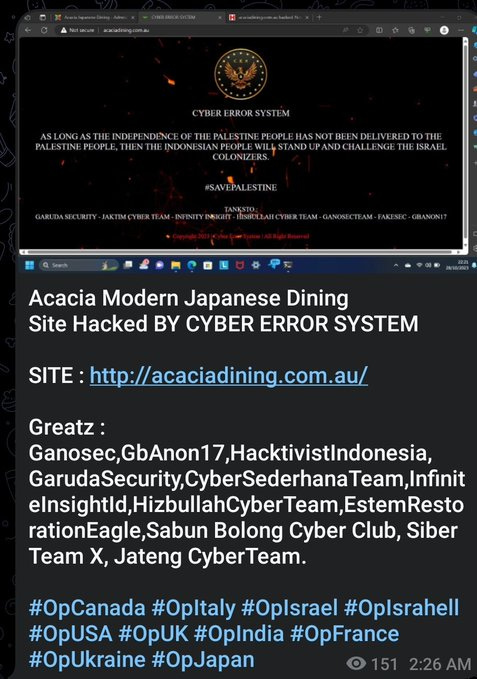
Cyber Error System defaced a small Japanese restaurant in Sydney. Another example of the types of websites hacktivists will target to deface, often small or medium business websites with limited cyber defence.
Ransomware - 3 Victims
20 October
Akira ransomware posted Protector Fire Services to their leak site.
25 October
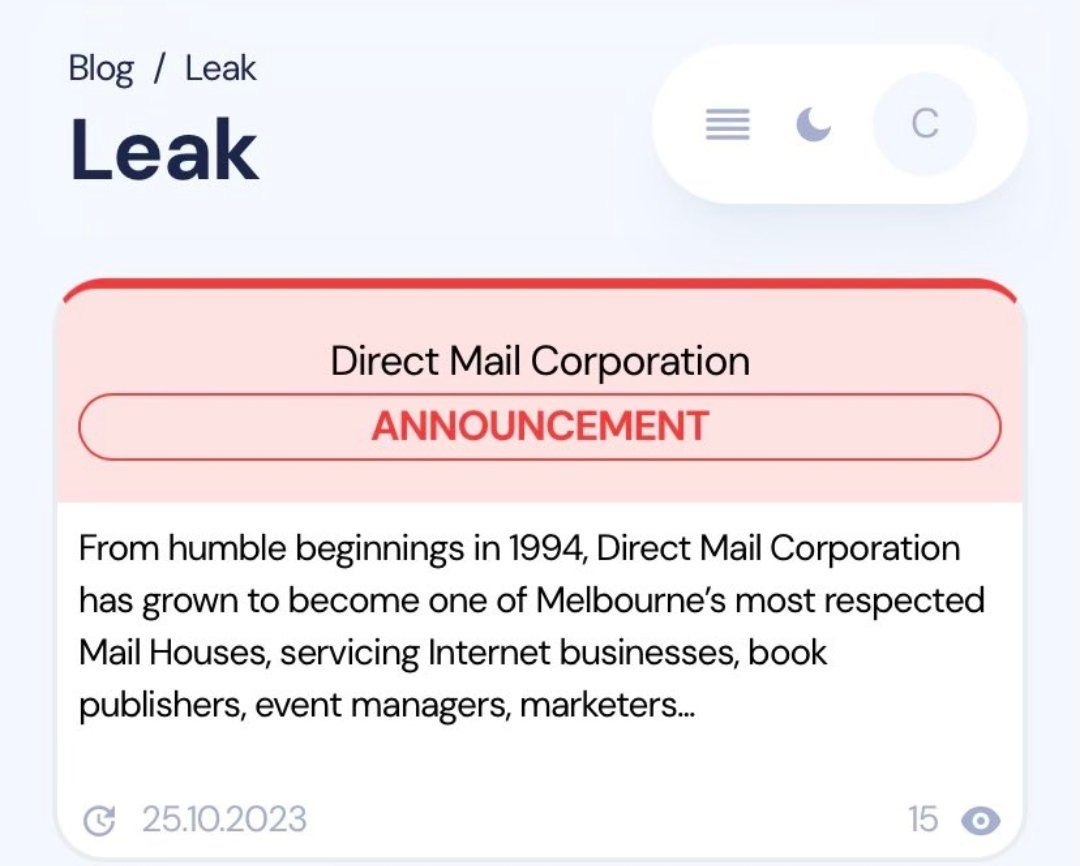
Inc Ransom posted Direct Mail Corporation to their leak site, the publishing house has hundreds of customers including state and federal government organization in Australia.
25 October
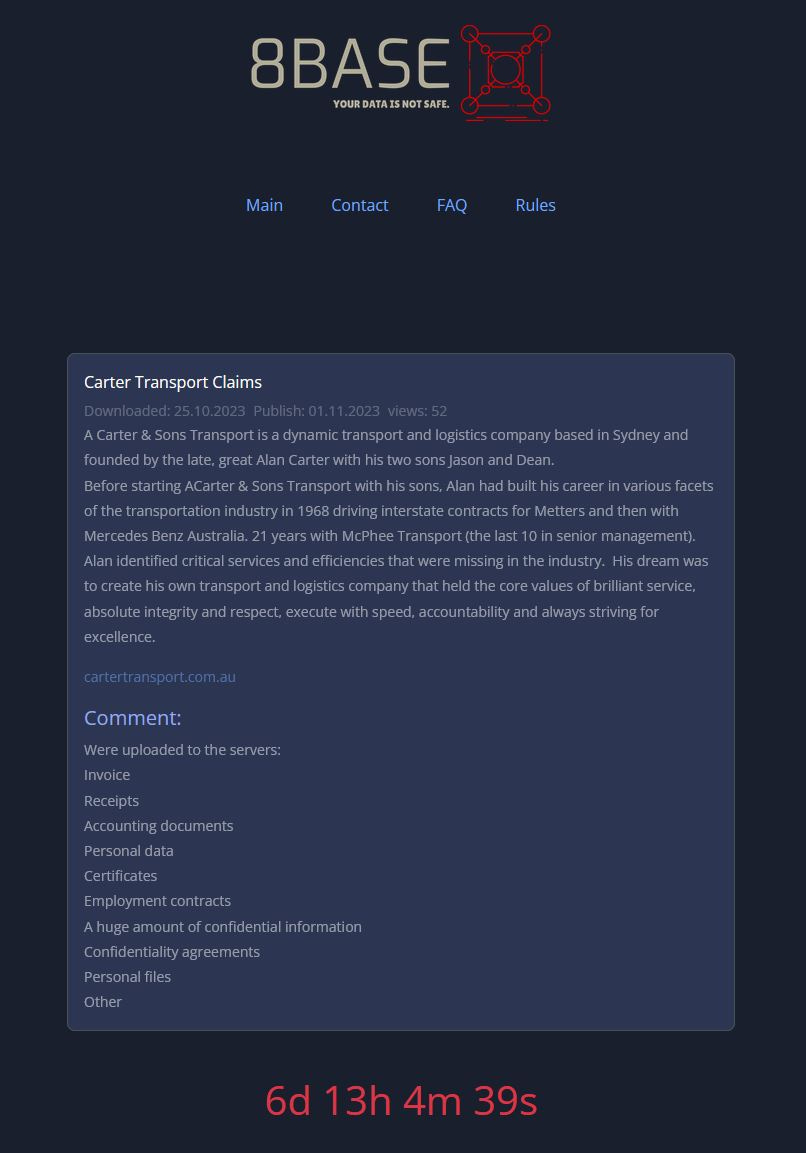
8Base posted Carter Transport Claims to their leak site.
Underground posts/mentions of note
16 October
Sovietmute, a member of the Russian-speaking forum XSS, advertised access to the Chainanalysis account of the Australian Government for $5000 USD. The seller indicated that access to the account would be exclusive to one buyer and, on 17 October, the access was sold. The threat actor has found success in selling access to SaaS platforms before, having sold access to the CRM of a South American debt collection agency earlier in October.
Chainanalysis is a SaaS platform that allows users to investigate the activity of cryptocurrency wallets on the blockchain. More specifically, Chainanalysis is commonly used by law enforcement to investigate fraud, money laundering, ransom payments and other financial criminal activity. It is unclear whether access to the Chainanalysis account will allow the buyer to snoop on current investigations.
24 October
CoreLab, a member of the Russian-speaking forum XSS, advertised Fortinet VPN access to an Australian military equipment manufacturer based in Tasmania, Australia. The seller claimed that the company has an annual revenue of $17.8 million, and specializes in propulsion systems for unmanned aerial vehicles (UAV). A day after the initial advertisement, CoreLab dropped the price from $900 to $400. CoreLab has a low reputation on XSS, with a negative reaction score and no prior sales listed on the forum. Threat actors that retain a low reputation over time will find it increasingly difficult to broker any successful sales of network access.
Media Reporting
The ABC has reported that thousands of South Australian public health patients are being contacted over a data breach of a patient portal run by the third-party Personify Care. The portal contained the health information of 121 patients on "supervised medication protocols", as well as evidence of them taking their medication that would be reviewed by doctors. The SA government also said the breach implicated the name and phone numbers of 12,624 patients. The breach had reportedly occurred due to human error that allowed a threat actor to delete a folder used to store patient documents uploaded to the Personify Care platform.
We have not seen any chatter or victim posting on underground forums that we monitor for the third-party company mentioned.
If you have any additional insights or questions please reach out to: