The following is an example of how you can review underground forum posts from Initial Access Brokers (IAB)s and get an understanding of who a possible victim could be. This is an example of a recent situation when an IAB post likely resulted in a ransomware attack on a victim.
I have not included the name of the victim organization, despite them being publicly posted to a ransomware leak site.
Hopefully these insights help analysts when monitoring underground forums for possible network breaches.
IAB posts Victim Access
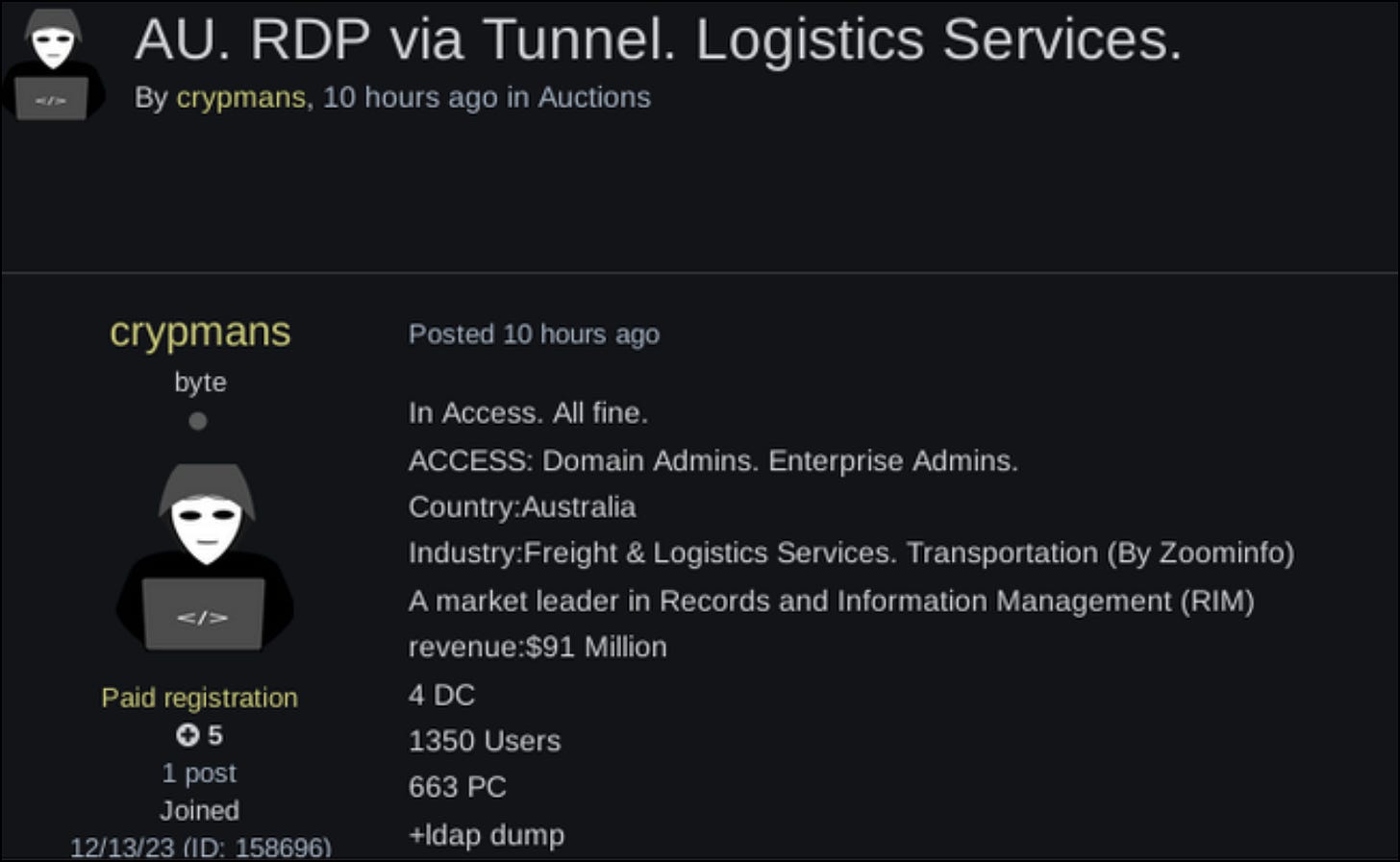
On 25 January, 2024 I saw an advertisement on Exploit Forum from an IAB who was selling access to an Australian company, at the time I saw the post it was already 10 hours old.
Crypmans, appears to have a good reputation on Exploit forum, this is highlighted by the fact that after I saw the post it was announced that it was sold within 6 hours. All up the Access was on sale for 16 hours.
Who is the victim organization?
Largely, IABs on underground forums use Zoominfo and Linkedin to source the information about victims and to provide context for the access they have on sale. Their goal is to provide enough information to entice the sale of the access, but not enough information that they will give away who the victim is. This balance can often give us the opportunity to discover who the victim is and provide some form of warning.
In the above image we can see that the IAB has provided us with two pieces of information about the organization.
Firstly, we check Linkedin to see if the blurb used by the IAB would match any organization. This can be done by simply posting the blurb into a search engine, or searching it via Linkedin.
I did this process and discovered that it did match an Australian organization, that does provide record and information management services.
The first piece of information:
A market leader in Records and Information Management (RIM)
This blurb is present in a Linkedin post for an Australian organization (Name removed)
At this point it appears we have a possible victim to link to the IAB post. However, we need to get further insights. For this I then checked Zoominfo to see if we could get another cross-referenced match.
The above image is taken from Zoominfo when we search for the same information as the Linkedin search, what we see is several overlaps with the original IAB post:
Freight & Logistics Services is mentioned by the IAB and on Zoominfo.
The IAB claims the organization has a revenue of $91 million, Zoominfo also tells us this organization has a revenue of $91 million.
As a result of reviewing the IAB information provided we have a moderate level of confidence that we know which organization has been posted to Exploit for sale.
Post by Ransomware gang.
Unfortunately, on 22 February 2024, the victim organization from this IAB post was posted to a ransomware leak site. (I have removed the victim name and also the ransomware groups name, I am sure most analysts will know the ransomware group from the style anyway.)
You will note that the blurb used by the ransomware gang is expanded on by the original IAB post, ransomware gangs also used Linkedin and Zoominfo to provide victim posting information.
Timeline of the incident
The following is a timeline of the events that resulted in a ransomware victim post:
IAB must have gained access to the victim organization prior to 16 January 2024.
IAB posts the victim for the first time on 16 January 2024 - there is lots of interest from forum users.
IAB removes the post on 19 January 2024 - Possible access issues.
IAB possibly regains access between 19 January and 25 January 2024.
IAB re-posts the victim on 25 January 2024 - Access is sold privately within 6 hours.
22 February 2024 - The victim is posted to a ransomware leak site.
Action this Intelligence
To action this intelligence you can do one, or both of the following:
Contact the organization directly - this might be difficult depending on how they offer communications and also on the credibility of yourself. (anonymous twitter accounts often get ignored - I know this from experience).
Contact your respective government authorities - they will often have a tip line, just make sure you provide as much detail as possible as they will no doubt be swamped with reports.
Summary
Threat analysts who monitor underground forums can often take the small pieces of information that IABs provide to do varied levels of reverse engineering to figure out who the victim organization is. While the victim network has already been impacted, the warning can provide a chance for an organization to take action in the window between IAB and ransomware exploitation.